This is a good opportunity as you cite for AU to roar and its member states to build internal capacity and allocate local resources - which includes development of the mega tech capabilities.
Legit or otherwise, the AU case is alleged over five years and said not to have been known or made known while elsewhere even school breaches warrant attention.
|
Society who in most cases seem oblivious as it gives out basic information and stores it, must take charge in re-defining what is Personal and what may afford to leak out or it is in the fate of developers and super hackers.
|
However, the best is when we put a money tag to it, it helps to make sense of it all and give due attention.
|
For instance who might be out there chunning and making play of data of a crucial provider such as KNH patient data or any other hospital, dispensary? Example of breach to Anthem in health.
12. Anthem
Date: February 2015
Impact: Theft of personal information on up to 78.8 million current and former customers.
Impact: Theft of personal information on up to 78.8 million current and former customers.
Fortune reported in January that a nationwide investigation concluded that a foreign government likely recruited the hackers who conducted what was said to be the largest data breach in healthcare history. It reportedly began a year before it was announced, when a single user at an Anthem subsidiary clicked on a link in a phishing email. The total cost of the breach is not yet known, but it is expected to exceed $100 million.
Be blessed.
Regards/Wangari
---
Pray God Bless. 2013Wangari circa - "Being of the Light, We are Restored Through Faith in Mind, Body and Spirit; We Manifest The Kingdom of God on Earth".
Pray God Bless. 2013Wangari circa - "Being of the Light, We are Restored Through Faith in Mind, Body and Spirit; We Manifest The Kingdom of God on Earth".
- Access Control
- Analytics
- Business Continuity
- Careers
- Data Loss Prevention
- Hacking
- IT Leadership
- Malware
- Physical Security
- Security
- Social Engineering
- News
- Features
- Insider
- How-Tos
- Blogs
- Resources/White Papers
- Newsletters
- Slideshows
- Video
- Dashboard
- Eve
- Home
- Hacking
- Data Breach
TODAY'S TOP STORIES
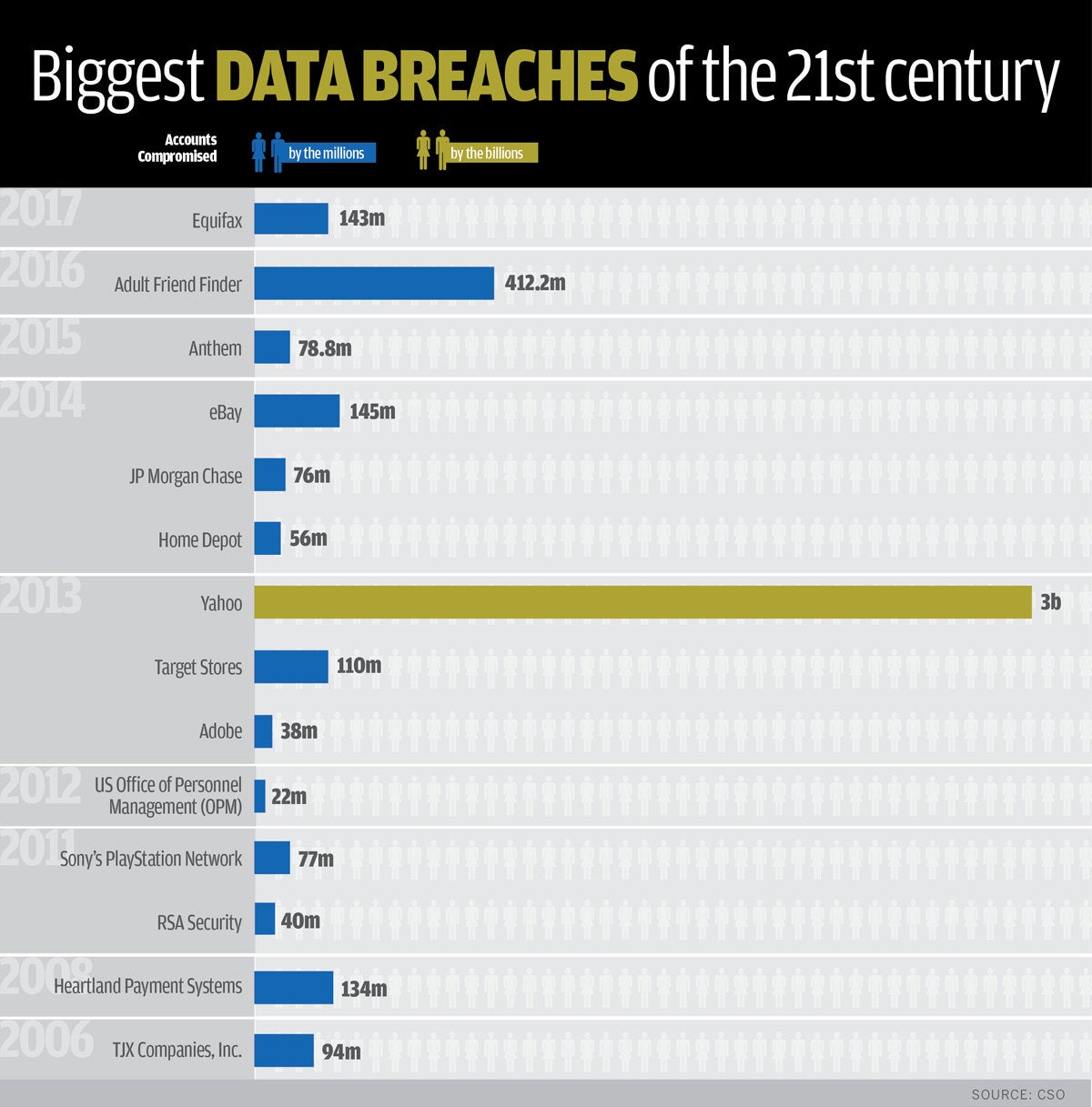
The 17 biggest data breaches of the 21st century
Security practitioners weigh in on the 17 worst data breaches in recent memory.
CSO | JAN 26, 2018 3:44 AM PT
The 16 worst data security breaches of the 21st century (5:24)
Data breaches happen daily, in too many places at once to keep count. But what constitutes a huge breach versus a small one? CSO compiled a list of 17 of the biggest or most significant breaches of the 21st century.
This list is based not necessarily on the number of records compromised, but on how much risk or damage the breach caused for companies, insurers and users or account holders. In some cases, passwords and other information were well protected by encryption, so a password reset eliminated the bulk of the risk.
[ How much does a data breach cost? Here's where the money goes. | Get the latest from CSO by signing up for our newsletters. ]
CSO1. Yahoo
Date: 2013-14
Impact: 3 billion user accounts
Details: In September 2016, the once dominant Internet giant, while in negotiations to sell itself to Verizon, announced it had been the victim of the biggest data breach in history, likely by “a state-sponsored actor,” in 2014. The attack compromised the real names, email addresses, dates of birth and telephone numbers of 500 million users. The company said the "vast majority" of the passwords involved had been hashed using the robust bcrypt algorithm.
Impact: 3 billion user accounts
Details: In September 2016, the once dominant Internet giant, while in negotiations to sell itself to Verizon, announced it had been the victim of the biggest data breach in history, likely by “a state-sponsored actor,” in 2014. The attack compromised the real names, email addresses, dates of birth and telephone numbers of 500 million users. The company said the "vast majority" of the passwords involved had been hashed using the robust bcrypt algorithm.
A couple of months later, in December, it buried that earlier record with the disclosure that a breach in 2013, by a different group of hackers had compromised 1 billion accounts. Besides names, dates of birth, email addresses and passwords that were not as well protected as those involved in 2014, security questions and answers were also compromised. In October of 2017, Yahoo revised that estimate, saying that, in fact, all 3 billion user accounts had been compromised.
The breaches knocked an estimated $350 million off Yahoo’s sale price. Verizon eventually paid $4.48 billion for Yahoo’s core Internet business. The agreement called for the two companies to share regulatory and legal liabilities from the breaches. The sale did not include a reported investment in Alibaba Group Holding of $41.3 billion and an ownership interest in Yahoo Japan of $9.3 billion.
Yahoo, founded in 1994, had once been valued at $100 billion. After the sale, the company changed its name to Altaba, Inc.
2. Adult Friend Finder
Date: October 2016
Impact: More than 412.2 million accounts
Details: The FriendFinder Network, which included casual hookup and adult content websites like Adult Friend Finder, Penthouse.com, Cams.com, iCams.com and Stripshow.com, was breached sometime in mid-October 2016. Hackers collected 20 years of data on six databases that included names, email addresses and passwords.
Impact: More than 412.2 million accounts
Details: The FriendFinder Network, which included casual hookup and adult content websites like Adult Friend Finder, Penthouse.com, Cams.com, iCams.com and Stripshow.com, was breached sometime in mid-October 2016. Hackers collected 20 years of data on six databases that included names, email addresses and passwords.
Most of the passwords were protected only by the weak SHA-1 hashing algorithm, which meant that 99 percent of them had been cracked by the time LeakedSource.com published its analysis of the entire data set on November 14.
CSO Online’s Steve Ragan reported at the time that, “a researcher who goes by 1x0123 on Twitter and by Revolver in other circles posted screenshots taken on Adult Friend Finder (that) show a Local File Inclusion vulnerability (LFI) being triggered.” He said the vulnerability, discovered in a module on the production servers used by Adult Friend Finder, “was being exploited.”
AFF Vice President Diana Ballou issued a statement saying, “We did identify and fix a vulnerability that was related to the ability to access source code through an injection vulnerability.”
3. eBay
Date: May 2014
Impact: 145 million users compromised
Details: The online auction giant reported a cyberattack in May 2014 that it said exposed names, addresses, dates of birth and encrypted passwords of all of its 145 million users. The company said hackers got into the company network using the credentials of three corporate employees, and had complete inside access for 229 days, during which time they were able to make their way to the user database.
Impact: 145 million users compromised
Details: The online auction giant reported a cyberattack in May 2014 that it said exposed names, addresses, dates of birth and encrypted passwords of all of its 145 million users. The company said hackers got into the company network using the credentials of three corporate employees, and had complete inside access for 229 days, during which time they were able to make their way to the user database.
It asked its customers to change their passwords, but said financial information, such as credit card numbers, was stored separately and was not compromised. The company was criticized at the time for a lack of communication informing its users and poor implementation of the password-renewal process.
CEO John Donahue said the breach resulted in a decline in user activity, but had little impact on the bottom line – its Q2 revenue was up 13 percent and earnings up 6 percent, in line with analyst expectations.
4. Equifax
Date: July 29 2017
Impact: Personal information (including Social Security Numbers, birth dates, addresses, and in some cases drivers' license numbers) of 143 million consumers; 209,000 consumers also had their credit card data exposed.
Details: Equifax, one of the largest credit bureaus in the U.S., said on Sept. 7, 2017 that an application vulnerability on one of their websites led to a data breach that exposed about 143 million consumers. The breach was discovered on July 29, but the company says that it likely started in mid-May.
5. Heartland Payment Systems
Date: March 2008
Impact: 134 million credit cards exposed through SQL injection to install spyware on Heartland's data systems.
Details: At the time of the breach, Heartland was processing 100 million payment card transactions per month for 175,000 merchants – most small- to mid-sized retailers. It wasn’t discovered until January 2009, when Visa and MasterCard notified Heartland of suspicious transactions from accounts it had processed.
Impact: 134 million credit cards exposed through SQL injection to install spyware on Heartland's data systems.
Details: At the time of the breach, Heartland was processing 100 million payment card transactions per month for 175,000 merchants – most small- to mid-sized retailers. It wasn’t discovered until January 2009, when Visa and MasterCard notified Heartland of suspicious transactions from accounts it had processed.
Among the consequences were that Heartland was deemed out of compliance with the Payment Card Industry Data Security Standard (PCI DSS) and was not allowed to process the payments of major credit card providers until May 2009. The company also paid out an estimated $145 million in compensation for fraudulent payments.
A federal grand jury indicted Albert Gonzalez and two unnamed Russian accomplices in 2009. Gonzalez, a Cuban-American, was alleged to have masterminded the international operation that stole the credit and debit cards. In March 2010 he was sentenced to 20 years in federal prison. The vulnerability to SQL injection was well understood and security analysts had warned retailers about it for several years. Yet, the continuing vulnerability of many Web-facing applications made SQL injection the most common form of attack against Web sites at the time.
6. Target Stores
Date: December 2013
Impact: Credit/debit card information and/or contact information of up to 110 million people compromised.
Details: The breach actually began before Thanksgiving, but was not discovered until several weeks later. The retail giant initially announced that hackers had gained access through a third-party HVAC vender to its point-of-sale (POS) payment card readers, and had collected about 40 million credit and debit card numbers.
Impact: Credit/debit card information and/or contact information of up to 110 million people compromised.
Details: The breach actually began before Thanksgiving, but was not discovered until several weeks later. The retail giant initially announced that hackers had gained access through a third-party HVAC vender to its point-of-sale (POS) payment card readers, and had collected about 40 million credit and debit card numbers.
By January 2014, however, the company upped that estimate, reporting that personally identifiable information (PII) of 70 million of its customers had been compromised. That included full names, addresses, email addresses and telephone numbers. The final estimate is that the breach affected as many as 110 million customers.
Target’s CIO resigned in March 2014, and its CEO resigned in May. The company recently estimated the cost of the breach at $162 million.
The company was credited with making significant security improvements. However, a settlement announced in May 2017 that gave Target 180 days to make specific security improvements was described by Tom Kellermann, CEO of Strategic Cyber Ventures and former CSO of Trend Micro, as a “slap on the wrist.” He also said it, “represents yesterday’s security paradigm,” since the requirements focus on keeping attackers out and not on improving incident response.
7. TJX Companies, Inc.
Date: December 2006
Impact: 94 million credit cards exposed.
Details: There are conflicting accounts about how this happened. One supposes that a group of hackers took advantage of a weak data encryption system and stole credit card data during a wireless transfer between two Marshall's stores in Miami, Fla. The other has them breaking into the TJX network through in-store kiosks that allowed people to apply for jobs electronically.
Impact: 94 million credit cards exposed.
Details: There are conflicting accounts about how this happened. One supposes that a group of hackers took advantage of a weak data encryption system and stole credit card data during a wireless transfer between two Marshall's stores in Miami, Fla. The other has them breaking into the TJX network through in-store kiosks that allowed people to apply for jobs electronically.
Albert Gonzalez, hacking legend and ringleader of the Heartland breach, was convicted in 2010 of leading the gang of thieves who stole the credit cards, and sentenced to 20 years in prison, while 11 others were arrested. He had been working as a paid informant for the US Secret Service, at a $75,000 salary at the time of the crimes. The government claimed in its sentencing memo that companies, banks and insurers lost close to $200 million.
8. Uber
Date: Late 2016
Impact: Personal information of 57 million Uber users and 600,000 drivers exposed.
Details: The scope of the Uber breach alone warrants its inclusion on this list, and it’s not the worst part of the hack. The way Uber handled the breach once discovered is one big hot mess, and it’s a lesson for other companies on what not to do.
Impact: Personal information of 57 million Uber users and 600,000 drivers exposed.
Details: The scope of the Uber breach alone warrants its inclusion on this list, and it’s not the worst part of the hack. The way Uber handled the breach once discovered is one big hot mess, and it’s a lesson for other companies on what not to do.
The company learned in late 2016 that two hackers were able to get names, email addresses, and mobile phone numbers of 57 users of the Uber app. They also got the driver license numbers of 600,000 Uber drivers. As far as we know, no other data such as credit card or Social Security numbers were stolen. The hackers were able to access Uber’s GitHub account, where they found username and password credentials to Uber’s AWS account. Those credentials should never have been on GitHub.
Here’s the really bad part: It wasn’t until about a year later that Uber made the breach public. What’s worse, they paid the hackers $100,000 to destroy the data with no way to verify that they did, claiming it was a “bug bounty” fee. Uber fired its CSO because of the breach, effectively placing the blame on him.
The breach is believed to have cost Uber dearly in both reputation and money. At the time that the breach was announced, the company was in negotiations to sell a stake to Softbank. Initially, Uber’s valuation was $68 billion. By the time the deal closed in December, its valuation dropped to $48 billion. Not all of the drop is attributable to the breach, but analysts see it being a significant factor.
9. JP Morgan Chase
Date: July 2014
Impact: 76 million households and 7 million small businesses
Details: The largest bank in the nation was the victim of a hack during the summer of 2014 that compromised the data of more than half of all US households – 76 million – plus 7 million small businesses. The data included contact information – names, addresses, phone numbers and email addresses – as well as internal information about the users, according to a filing with the Securities and Exchange Commission.
Impact: 76 million households and 7 million small businesses
Details: The largest bank in the nation was the victim of a hack during the summer of 2014 that compromised the data of more than half of all US households – 76 million – plus 7 million small businesses. The data included contact information – names, addresses, phone numbers and email addresses – as well as internal information about the users, according to a filing with the Securities and Exchange Commission.
The bank said no customer money had been stolen and that there was “no evidence that account information for such affected customers – account numbers, passwords, user IDs, dates of birth or Social Security numbers – was compromised during this attack."
Still, the hackers were reportedly able to gain “root" privileges on more than 90 of the bank’s servers, which meant they could take actions including transferring funds and closing accounts. According to the SANS Institute, JP Morgan spends $250 million on security every year.
In November 2015, federal authorities indicted four men, charging them with the JP Morgan hack plus other financial institutions. Gery Shalon, Joshua Samuel Aaron and Ziv Orenstein faced 23 counts, including unauthorized access of computers, identity theft, securities and wire fraud and money laundering that netted them an estimated $100 million. A fourth hacker who helped them breach the networks was not identified.
Shalon and Orenstein, both Israelis, pleaded not guilty in June 2016. Aaron was arrested at JFK Airport in New York last December.
10. US Office of Personnel Management (OPM)
Date: 2012-14
Impact: Personal information of 22 million current and former federal employees
Details: Hackers, said to be from China, were inside the OPM system starting in 2012, but were not detected until March 20, 2014. A second hacker, or group, gained access to OPM through a third-party contractor in May 2014, but was not discovered until nearly a year later. The intruders exfiltrated personal data – including in many cases detailed security clearance information and fingerprint data.
Impact: Personal information of 22 million current and former federal employees
Details: Hackers, said to be from China, were inside the OPM system starting in 2012, but were not detected until March 20, 2014. A second hacker, or group, gained access to OPM through a third-party contractor in May 2014, but was not discovered until nearly a year later. The intruders exfiltrated personal data – including in many cases detailed security clearance information and fingerprint data.
Last year, former FBI director James Comey spoke of the information contained in the so-called SF-86 form, used for conducting background checks for employee security clearances. “My SF-86 lists every place I’ve ever lived since I was 18, every foreign travel I’ve ever taken, all of my family, their addresses,” he said. “So it’s not just my identity that’s affected. I’ve got siblings. I’ve got five kids. All of that is in there.”
A report, released last fall by the House Committee on Oversight and Government Reform summed up the damage in its title: “The OPM Data Breach: How the Government Jeopardized Our National Security for More than a Generation.”
11. Sony's PlayStation Network
Date: April 20, 2011
Impact: 77 million PlayStation Network accounts hacked; estimated losses of $171 million while the site was down for a month.
Details: This is viewed as the worst gaming community data breach of all-time. Of more than 77 million accounts affected, 12 million had unencrypted credit card numbers. Hackers gained access to full names, passwords, e-mails, home addresses, purchase history, credit card numbers and PSN/Qriocity logins and passwords. "It's enough to make every good security person wonder, 'If this is what it's like at Sony, what's it like at every other multi-national company that's sitting on millions of user data records?'" said eIQnetworks' John Linkous. He says it should remind those in IT security to identify and apply security controls consistently across their organizations. For customers, "Be careful whom you give your data to. It may not be worth the price to get access to online games or other virtual assets."
Impact: 77 million PlayStation Network accounts hacked; estimated losses of $171 million while the site was down for a month.
Details: This is viewed as the worst gaming community data breach of all-time. Of more than 77 million accounts affected, 12 million had unencrypted credit card numbers. Hackers gained access to full names, passwords, e-mails, home addresses, purchase history, credit card numbers and PSN/Qriocity logins and passwords. "It's enough to make every good security person wonder, 'If this is what it's like at Sony, what's it like at every other multi-national company that's sitting on millions of user data records?'" said eIQnetworks' John Linkous. He says it should remind those in IT security to identify and apply security controls consistently across their organizations. For customers, "Be careful whom you give your data to. It may not be worth the price to get access to online games or other virtual assets."
In 2014, Sony agreed to a preliminary $15 million settlement in a class action lawsuit over the breach.
12. Anthem
Date: February 2015
Impact: Theft of personal information on up to 78.8 million current and former customers.
Details: The second-largest health insurer in the U.S., formerly known as WellPoint, said a cyberattack had exposed the names, addresses, Social Security numbers, dates of birth and employment histories of current and former customers – everything necessary to steal identity.
Impact: Theft of personal information on up to 78.8 million current and former customers.
Details: The second-largest health insurer in the U.S., formerly known as WellPoint, said a cyberattack had exposed the names, addresses, Social Security numbers, dates of birth and employment histories of current and former customers – everything necessary to steal identity.
Fortune reported in January that a nationwide investigation concluded that a foreign government likely recruited the hackers who conducted what was said to be the largest data breach in healthcare history. It reportedly began a year before it was announced, when a single user at an Anthem subsidiary clicked on a link in a phishing email. The total cost of the breach is not yet known, but it is expected to exceed $100 million.
Anthem said in 2016 that there was no evidence that members' data have been sold, shared or used fraudulently. Credit card and medical information also allegedly has not been taken.
On Tuesday, 30 January 2018, 7:37, Mwendwa Kivuva via kictanet <kictanet@lists.kictanet.or.ke> wrote:
The #sittingducks really we are. #NoFreeLunch. Colonization 3.0. Africa shall be colonized by all other nations because of lack of leadership and integrity. We are owned. Sold. African leaders should have a little pride in themselves. Just a little. And for starters Africa should bring down that edifice from Beijing. His excellency Paul Kagame, the assembly chair has shown a lot of independent in his thinking. He should champion the demolition, and look for other African bred solution for a new building. From Carthage to Maseru, Nouakchott to Mogadishu, we must have competence to stamp our feet on the ground. Show we mean business. There is no way we can achieve vision 2063 while we are slaves. $200m is a tinny sum that cannot even get into the balance sheet of some African countries.
On Jan 30, 2018 3:16 AM, "Ali Hussein via kictanet" <kictanet@lists.kictanet.or.ke > wrote:
ListersSomething most of us suspected is happening seems to be happening at the Apex of African Government.John Aglionby, East Africa Correspondent, and Emily Feng and Yuan Yang in BeijingAfrican Union officials have accused China of hacking its headquarters’ computer systems every night for five years and downloading confidential data. Beijing funded the AU’s $200m building in Addis Ababa, Ethiopia, while a Chinese state-owned company built it.Analysts said the fact that the hack remained secret for a year after being discovered and that the AU was not commenting publicly demonstrated China’s dominant relationships with African states.The data theft was exposed by French newspaper Le Monde Afrique and confirmed to the Financial Times on Monday. China denied the accusation.The hack underscores the risk African nations take in allowing Chinese technology companies such prominent roles in developing their telecoms backbones, despite the US placing restrictions on investment by Huawei and ZTE.The two companies have “built most of Africa’s telecoms infrastructure”, according to a McKinsey report on Chinese investment in Africa published last year titled Dance of the Lions and Dragons.Le Monde reported that data transfer activity was at a peak every night between midnight and 2am from January 2012, when the building was inaugurated, to January 2017.AU technicians discovered the organisation’s secrets were being copied on to servers in Shanghai, according to the article.The AU has now acquired its own servers and all electronic communication is now encrypted and no longer passes through Ethio Telecom, Ethiopia’s state-run operator. Other enhanced security features have also been installed.Aly-Khan Satchu, an investment analyst in Nairobi, said the hack was “really alarming”, partly because it exposed that “African countries have no leverage over China”.He added: “There’s this theory in Africa that China is Santa Claus. It isn’t. Our leaders need to be disavowed of that notion.”China’s ministry of foreign affairs denied the hacking allegations, calling the reports “baseless” and “complete nonsense”.“China would in no way interfere with the internal policies of African countries or do anything that would hurt their interests,” it said in a statement on Monday.AU spokespeople declined to comment but an African diplomat attending the AU’s annual heads of government summit on Monday said there “would be a lot of anger over this”. “This is not the sort of thing Africans will entertain and take lightly,” he said.However, a western diplomat based in the region said the AU should not have been surprised considering China built and fitted out the 19-storey building that dominates the Addis Ababa skyline.“When you let them build the whole system, of course they are listening in,” the diplomat said.One AU official said there were “many issues with the building that are still being resolved with the Chinese. It’s not just cyber security.”China State Construction Engineering Corporation, the state-owned company that built the headquarters, could not be reached for comment. Anhui Foreign Economic Construction Company, the developer of another building on the AU headquarters site, said it had not seen the report and declined to comment.Xi Jinping, the Chinese president, promised $60bn in investment and aid to African countries at his last summit with African leaders, in South Africa two years ago. Chinese companies have built much of the road and rail infrastructure across the continent and more than 10,000 Chinese companies are active in the region, according to the McKinsey report.“There is no other country with such depth and breadth of engagement in Africa across the dimensions of trade, investment, infrastructure financing, and aid,” the consultancy’s report said.However, concerns about technological backdoors in Chinese tech hardware led US policymakers in 2012 to recommend blocking acquisition attempts from ZTE and Huawei.Huawei has repeatedly been barred from making acquisitions in the US over national security concerns. This month, American carrier AT&T dropped its deal with Huawei to distribute Chinese-made handsets in the US.Le Monde also reported that GCHQ, the British government listening agency, had intercepted communications between AU and UN officials in 2009 and 2010, citing documents released by US whistleblower Edward Snowden.#SittingDucks..That's what we are.Ali HusseinPrincipalHussein & AssociatesTel: +254 713 601113Twitter: @AliHKassimSkype: abu-jomoLinkedIn: http://ke.linkedin.com/in/ alihkassim13th Floor , Delta Towers, Oracle Wing,Chiromo Road, Westlands,Nairobi, Kenya.
Any information of a personal nature expressed in this email are purely mine and do not necessarily reflect the official positions of the organizations that I work with.
______________________________ _________________
kictanet mailing list
kictanet@lists.kictanet.or.ke
https://lists.kictanet.or.ke/ mailman/listinfo/kictanet
Twitter: http://twitter.com/kictanet
Facebook: https://www.facebook.com/ KICTANet/
Unsubscribe or change your options at https://lists.kictanet.or.ke/ mailman/options/kictanet/ kivuva%40transworldafrica.com
The Kenya ICT Action Network (KICTANet) is a multi-stakeholder platform for people and institutions interested and involved in ICT policy and regulation. The network aims to act as a catalyst for reform in the ICT sector in support of the national aim of ICT enabled growth and development.
KICTANetiquette : Adhere to the same standards of acceptable behaviors online that you follow in real life: respect people's times and bandwidth, share knowledge, don't flame or abuse or personalize, respect privacy, do not spam, do not market your wares or qualifications.
_______________________________________________
kictanet mailing list
kictanet@lists.kictanet.or.ke
https://lists.kictanet.or.ke/mailman/listinfo/kictanet
Twitter: http://twitter.com/kictanet
Facebook: https://www.facebook.com/KICTANet/
Unsubscribe or change your options at https://lists.kictanet.or.ke/mailman/options/kictanet/wangarikabiru%40yahoo.co.uk
The Kenya ICT Action Network (KICTANet) is a multi-stakeholder platform for people and institutions interested and involved in ICT policy and regulation. The network aims to act as a catalyst for reform in the ICT sector in support of the national aim of ICT enabled growth and development.
KICTANetiquette : Adhere to the same standards of acceptable behaviors online that you follow in real life: respect people's times and bandwidth, share knowledge, don't flame or abuse or personalize, respect privacy, do not spam, do not market your wares or qualifications.
kictanet mailing list
kictanet@lists.kictanet.or.ke
https://lists.kictanet.or.ke/mailman/listinfo/kictanet
Twitter: http://twitter.com/kictanet
Facebook: https://www.facebook.com/KICTANet/
Unsubscribe or change your options at https://lists.kictanet.or.ke/mailman/options/kictanet/wangarikabiru%40yahoo.co.uk
The Kenya ICT Action Network (KICTANet) is a multi-stakeholder platform for people and institutions interested and involved in ICT policy and regulation. The network aims to act as a catalyst for reform in the ICT sector in support of the national aim of ICT enabled growth and development.
KICTANetiquette : Adhere to the same standards of acceptable behaviors online that you follow in real life: respect people's times and bandwidth, share knowledge, don't flame or abuse or personalize, respect privacy, do not spam, do not market your wares or qualifications.